How to Crack Software by Modifying DLL Files: 7 Steps
€ 38.00 · 4.5 (294) · In Magazzino

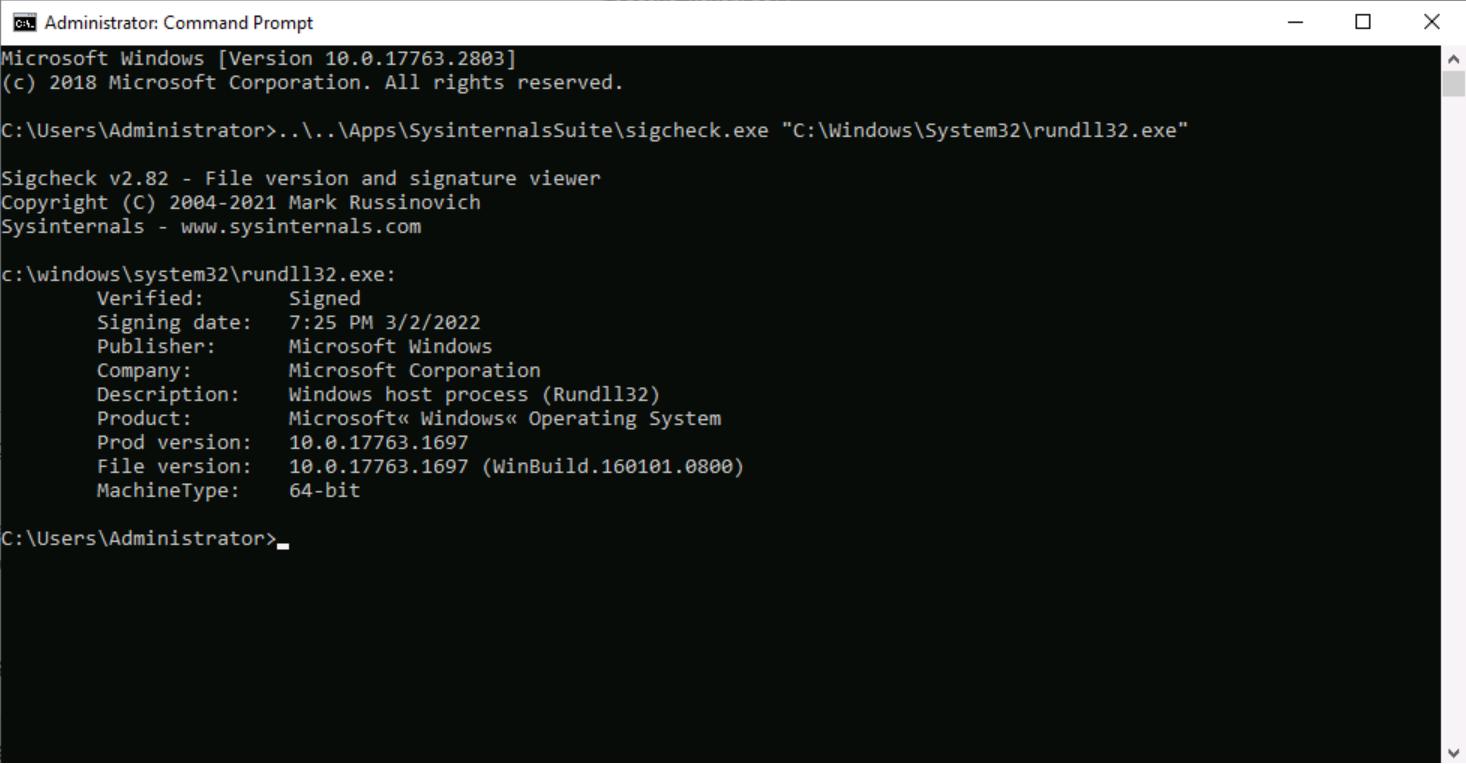
Rundll32: The Infamous Proxy for Executing Malicious Code

Threat Simulator: June 2023 Update
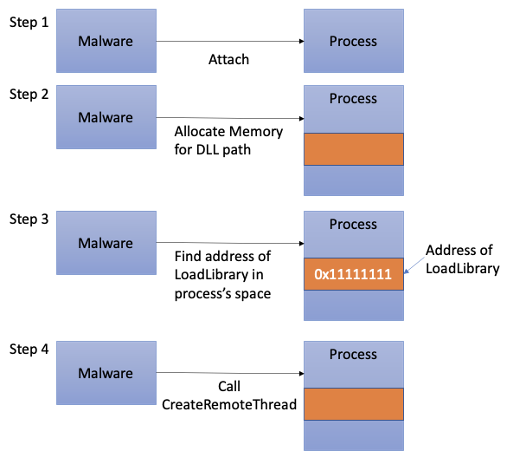
Process Injection Techniques used by Malware, by Angelystor, CSG @ GovTech
HOW TO CRACK SOFTWARE?? – Alienicktech

What is DLL Hijacking? - GeeksforGeeks
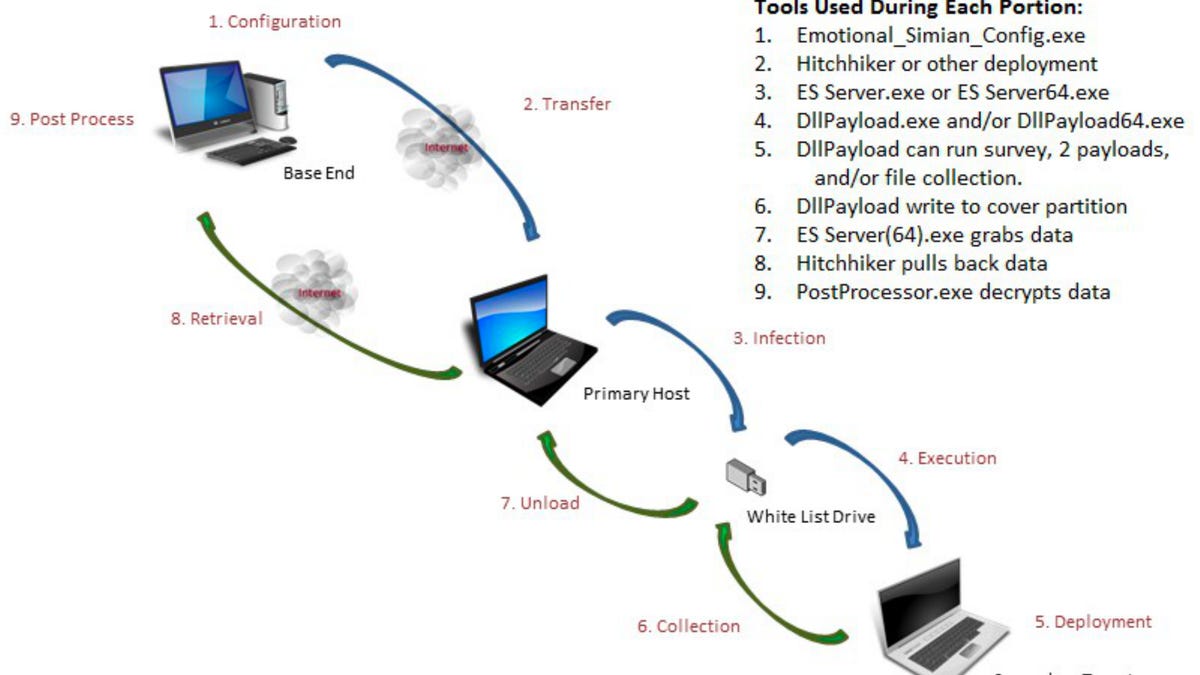
WikiLeaks: The CIA can remotely hack into computers that aren't even connected to the internet

DLL Side-loading & Hijacking DLL Abuse Techniques Overview
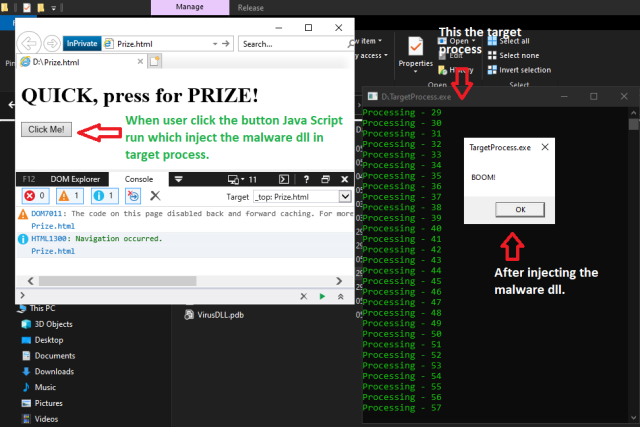
Inject DLL in Another Process using C++ Win32 Windows API - CodeProject
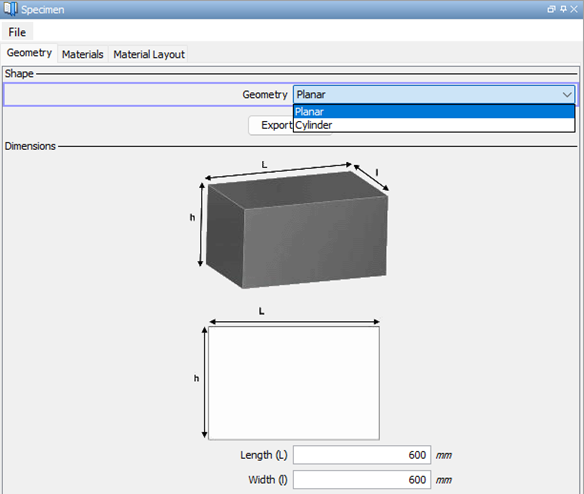
CIVA - Tips
![]()
Resource Hacker
How To Decompile .NET Applications (Easy)✓

Learn to Edit DLL Files
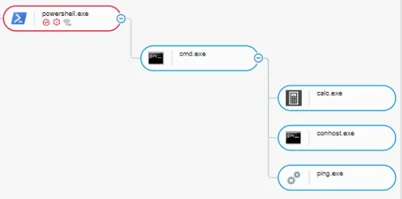
THREAT ANALYSIS REPORT: DLL Side-Loading Widely (Ab)Used